by Redacción | 29/06/2016 | English
Opinion: We are in the midst of a new economic and technological era, often referred to as “The Fourth Industrial Revolution” or “Industry 4.0.” Smart, connected, and responsive technologies are merging with environments that are becoming more data-rich, and, as a result, digital disruption to more traditional business models is becoming the norm, not the exception.

by Redacción | 28/06/2016 | English
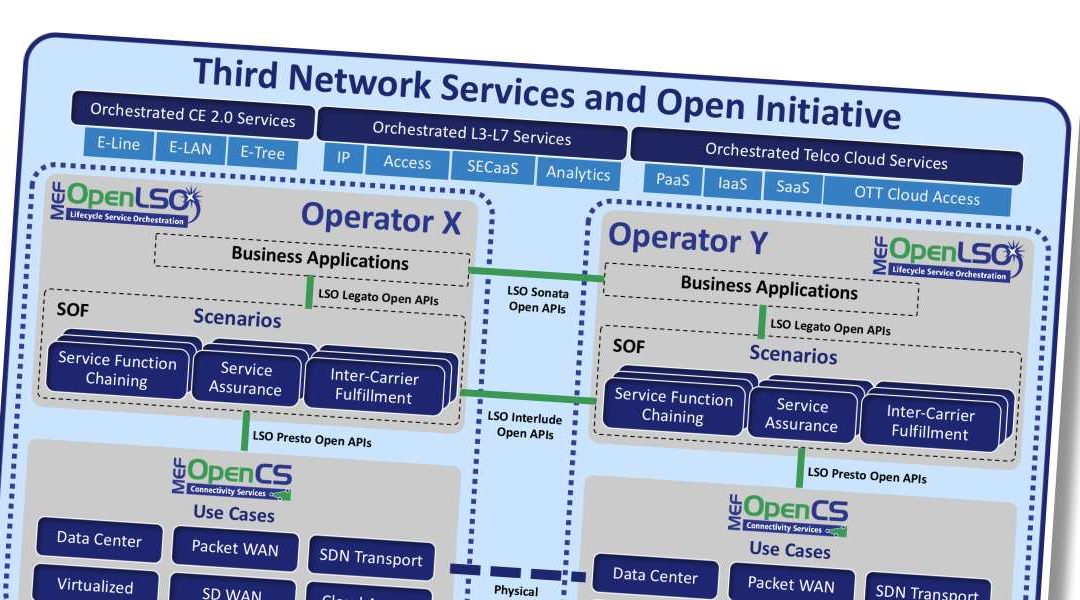
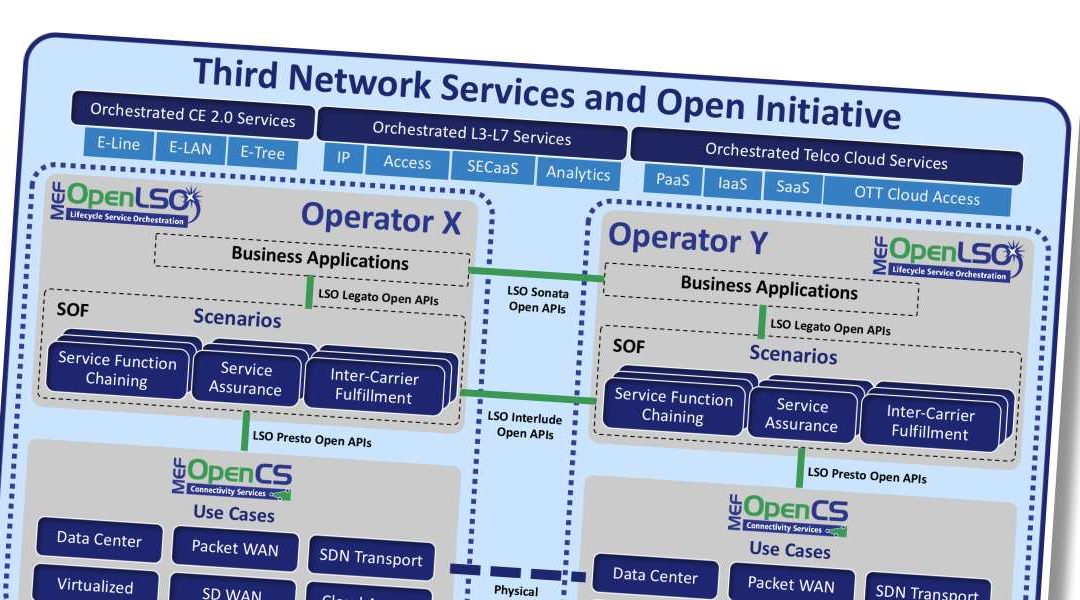
Open standards and open source projects are both essential ingredients for advancing the cause of interoperable next-generation carrier networks.
by Redacción | 28/06/2016 | English
MEF Publishes Euro16 LSO Hackathon Report & Prepares For MEF16 LSO Hackathon In Baltimore On 7-9 November 2016.

by Redacción | 23/06/2016 | English
Cylance establishes partnerships in France, Germany and the Middle East to meet rising demands in EMEA for preventive cybersecurity solutions and services.

by Redacción | 08/06/2016 | English
Gartner, Inc. said global smartphone sales will continue to slow and will no longer grow in double digits. Worldwide smartphone sales are expected to grow 7 per cent in 2016 to reach 1.5 billion units. This is down from 14.4 per cent growth in 2015. In 2020, smartphone sales are on pace to total 1.9 billion units.

by Redacción | 27/04/2016 | English
Opinion: The tech world is witnessing a turning point. Apple saw the first decline in its sales and profits in 13 years, triggering a selloff in the financial market that wiped out $43 billion of the company’s market value. Such is the rough-and-tumble play of the high-tech world.

by Redacción | 27/04/2016 | English
According to the latest preliminary release from the International Data Corporation (IDC) Worldwide Quarterly Mobile Phone Tracker, vendors shipped a total of 334.9 million smartphones worldwide in the first quarter of 2016 (1Q16), up slightly from the 334.3 million units in 1Q15, marking the smallest year-over-year growth on record.
by Redacción | 27/04/2016 | English
Expert Services From Datavision Will Benefit MEF Members And Accelerate Agile, Assured & Orchestrated Third Network Services.
by Redacción | 18/04/2016 | English
To Demonstrate How LSO, SDN, NFV & CE 2.0 Can Be Combined To Enable Dynamic, Assured & Orchestrated Third Network Services.

by Redacción | 15/04/2016 | English
Telco and tech firms spent over US$31bn on IoT-related investments and acquisitions between 2011 and 2015, according to new research from Ovum.