by Redacción | 28/07/2017 | English
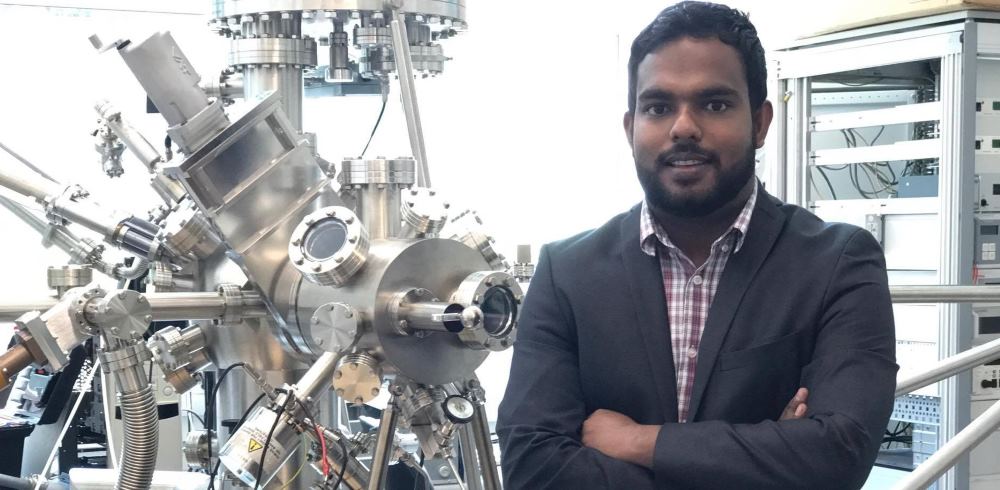
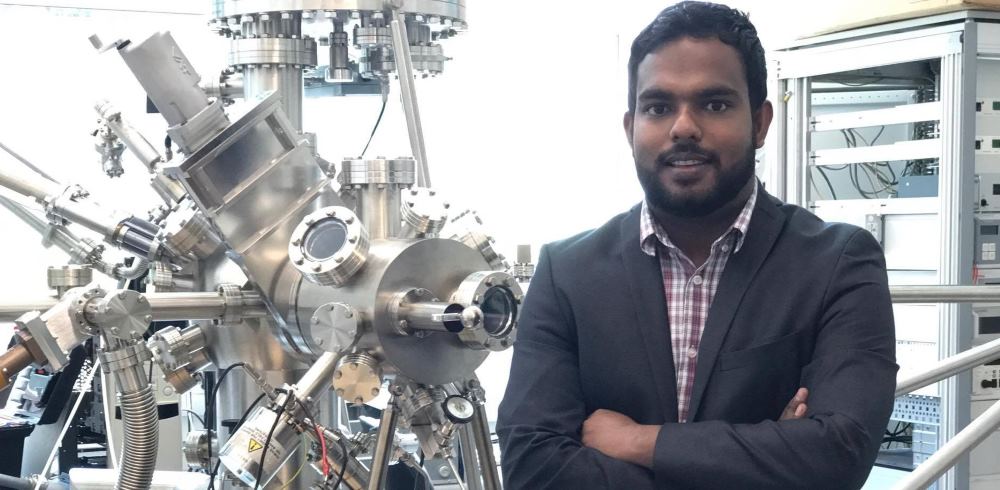
The University of Surrey is developing a revolutionary technology that will allow people to act as their own “power source” by wearing clothing such as “smart” shirts and shoes that harvest and store electricity. The wearable power sources are Triboelectric Nanogenerators (TENGs), energy harvesting devices, which convert the movements of materials that produce static charge into usable electricity.

by Redacción | 11/07/2017 | English
Infinera, a provider of Intelligent Transport Networks, announced the successful completion of a subsea field trial with a major subsea network provider on a modern trans-Atlantic route.
by Redacción | 11/07/2017 | English
Worldwide semiconductor revenue is forecast to total $401.4 billion in 2017, an increase of 16.8 per cent from 2016, according to Gartner, Inc. This will be the first time semiconductor revenue has surpassed $400 billion. The market reached the $300 billion milestone seven years ago, in 2010, and surpassed $200 billion in 2000.

by Redacción | 21/03/2017 | English
Infinera, a provider of Intelligent Transport Networks, introduced Infinera Instant Network, the next generation of software-defined capacity (SDC) for cloud scale networks and building the necessary foundation for cognitive networking.

by Redacción | 20/03/2017 | English
CHT Global (Chunghwa Telecom Global, Inc.) today announced the launch of CHT Global Software-Defined Wide Area Network (SD-WAN) on a global scale that will enable enterprises to easily transition from traditional static hardware to software-based WAN.

by Redacción | 15/03/2017 | English
Cybercriminals want your credentials and your employees’ credentials. When those hackers succeed in stealing that information, it can be bad for individuals – and even worse for corporations and other organizations. This is a scourge that’s bad, and it will remain bad.

by Redacción | 14/02/2017 | English
AV-TEST compares Cylance against five signature-based antivirus software suites; Results show Cylance with more than 97 percent efficacy against unknown threats versus a 42 percent average by legacy AV vendors.

by Redacción | 02/02/2017 | English
Cylance is experiencing unprecedented momentum in the past few years, achieving 322 percent growth in 2015 and 607 percent growth in 2016.

by Redacción | 18/01/2017 | English
Opinion: Not that long ago, hackers emerged as modern-day Robin Hoods, digital heroes who relentlessly uncovered weaknesses in applications and networks to reveal the dangers of using technology carelessly. They are curious, provocative; love to know how things work and how they can be improved. Today, however, there is blight on their good name.

by Redacción | 18/01/2017 | English
Opinion: Signature databases, distributed by antivirus/malware researchers and companies, are an imperfect method for several reasons. As the number of malware variants increase, so do the number of signatures – and this takes more time to process. Also, signatures are of limited use against zero-day attacks that nobody has seen before.